SMS Bombing is a prank which is often played in which we send continuous text messages to the victim. The number of texts may vary from 15-20 to even 1000 ! So, I'll be sharing a method of sms bombing here and this method does not use any software to bomb, rather a bit of innovation with a plug-in.
Requirements : 1.Mozilla . It can be downloaded here.
2.A Mozilla plug-in named Imacros. Add it to firefox from here.
3.A site which allow you to send text messages with no captcha challenge and no adds
between to successive messages you send.
Make sure you have installed imacros correctly and to get an icon like shown in the below.
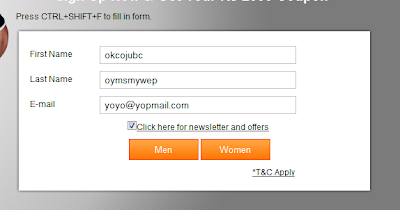
Method : 1.Go to the site you are using to send texts.Log in there.
2.Now click on the icon of imacros from there click on "rec" and then "record".Please make
sure that all tabs are closed click on record button.
2.Now click on the icon of imacros from there click on "rec" and then "record".Please make
sure that all tabs are closed click on record button.
3.Now type the number of the victim and then the message.
4.Click on "send"button.
5.As the delivery report comes,click on "send another message".
6.After clicking on send another message click on "stop" button in imacros.
7.Now click on "play" option in imacros.
8.You will see an option Repeat Macros.There,let the"current" be one and in "max" column
the number of messages you want to bomb.
9.Now click on "play(loop)".
10.Messages will be bombed ! Happy bombing :P
p.s.It is on you to find site which is vulnerable to this.I have just shared the method.
Note : SMS Bombing and SMS spoofing is illegal in and many other countries.So I don't take any responsibility for any misuse.This tutorial in Only for educational purposes.